The art of lock picking is a hobby commonly found among cyber security professionals, enthusiasts and hobbyists.
Hackers tend to love defeating locking mechanisms. Similarly to the digital world, you are tasked to identify vulnerabilities and exploit flaws in systems. It is undoubtable that this is a very suitable hobby for many in the security domain.
However I find browsing the current lock picking market a daunting exercise. Even though you can easily find what equipment you need to create your first toolbox, the pricing for common "quality" products is - in my opinion - very high and such expensive solution might discourage new enthusiasts who just want to try out a new hobby.
As a result, for the last couple of months, I've been quality testing cheap chinese locksmith tools aiming to find affordable and acceptable solutions for begginer lock pickers.
Brief Introduction
While movies and popular culture often portray lockpicking as a mysterious or illicit art, in reality it is an important aspect of physical security research. "Ethical" practitioners use it to test and improve locks, helping manufacturers identify weaknesses before they can be exploited maliciously. Over time it also became associated with curiosity and skill-based hobbies, such as those practiced by security enthusiasts who study locks to better understand how they work and how to design stronger security systems.
This article is not intended to be a comprehensive or authoritative guide to lock picking. Instead, its goal is to introduce newcomers to common lock profiles, outline basic manipulation and bypass concepts, and present a selection of affordable tools suitable for experimentation and learning. The focus is on accessibility rather than mastery highlighting what types of tools exist, what problems they are designed to solve, and how a budget-conscious beginner might explore the field without a significant financial commitment.
By the end of this article, you should understand common lock types, the basic manipulation approaches used against them, and how to assemble a functional toolkit on a budget.

Common Lock Types
In everyday life, several lock designs are widely encountered due to their balance of security, simplicity, and cost. These mechanisms form the basis of most residential, commercial, and portable locking systems. Common lock profiles include:
Pin Tumbler Locks:
Perhaps the most familiar and widely used lock type in the world, pin tumbler locks rely on a series of spring-loaded pins that must be lifted to specific heights by the correct key before the lock will turn.

Standard Pin Tumbler Lock
The main components of a standard pin-tumbler lock mechanism are the following:
-
Shell (Green):
- The outer housing of the lock, a stationary body around the plug keeping the internal mechanisms.
-
Plug (Light Yellow)
- The rotating core of the lock into which the key is inserted. A cam or tailpiece attached to the rear of the plug converts rotation into movement of the locking bolt or latch.
- The interface between the plug and the shell is known as the shear line, which must remain clear for the plug to rotate.
-
Key Pins (Red lower pins)
- The pins that rest directly on the key. They vary in length according to the key's cut depths and remain entirely within the plug when the correct key is inserted.
-
Driver Pins (Purple upper pins)
- Positioned above the key pins, these pins extend into the shell when the lock is in the closed position, blocking the shear line and preventing rotation. When the correct key is inserted, the driver pins are lifted completely into the shell, freeing the plug.
-
Springs (Coils)
- Located above the driver pins, the springs apply consistent downward pressure to the pin stacks, ensuring reliable engagement with the key and stable operation of the lock.
-
Pin Chambers
- Vertical bores drilled through both the shell and the plug. These chambers guide the pin stacks and maintain their alignment during operation.
When no key is inserted, the driver pins are forced downward by their springs. This causes each driver pin to extend across the boundary between the plug and the lock body, mechanically blocking the plug from rotating.
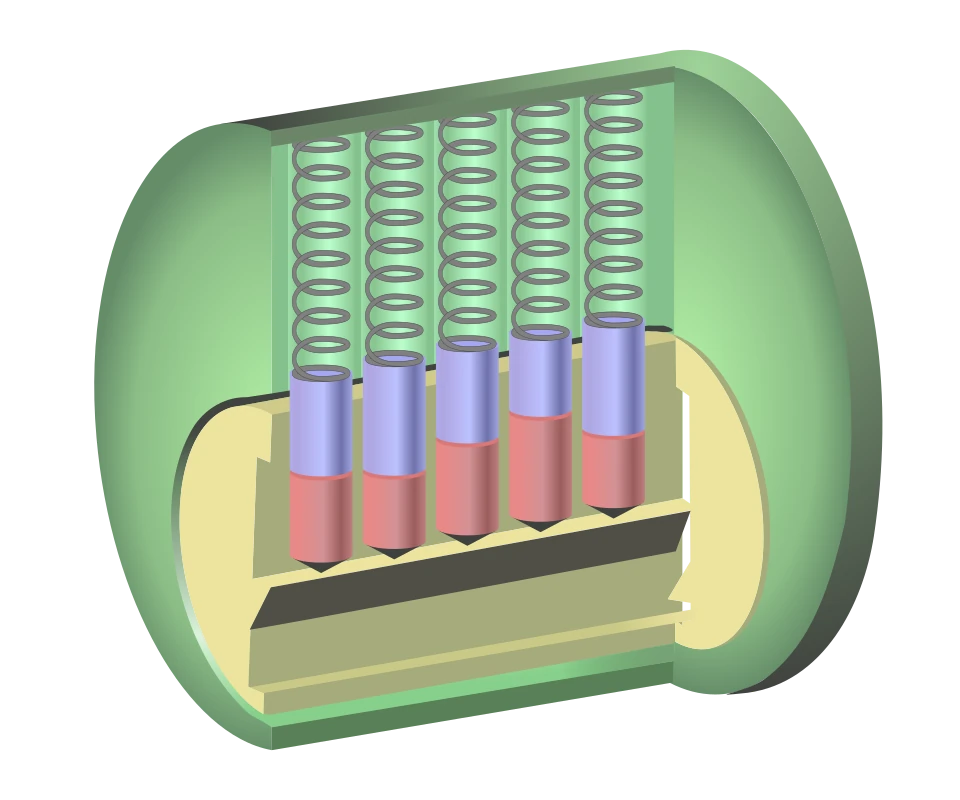
Pin Tumbler No Key Inserted
When the correct key is inserted, the shaped cuts on the key lift each key pin to a specific height. At this position, the boundary between the key pins and the driver pins aligns precisely with the edge of the plug, known as the shear line.
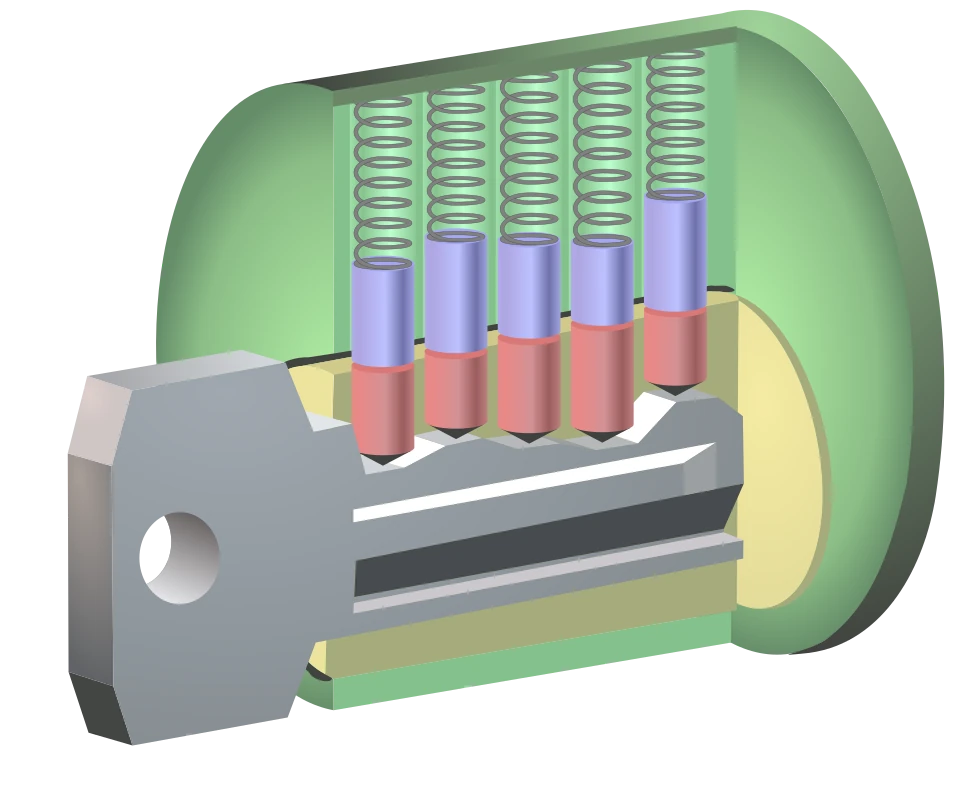
Pin Tumbler With Key Inserted
With all pin pairs correctly aligned at the shear line, the driver pins are fully contained within the lock body, leaving the plug unobstructed. This allows the plug to rotate freely, retracting the locking mechanism and opening the lock.
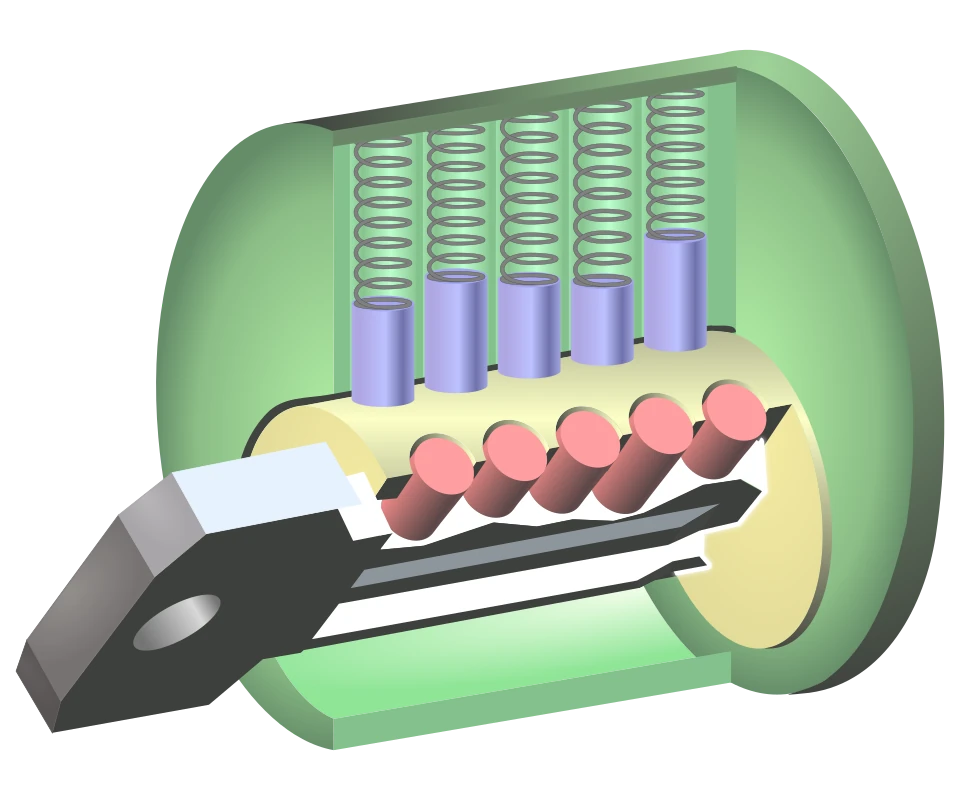
Pin Tumbler Unlocked
Wafer Tumbler Locks:
Similar in concept to pin tumblers but using flat wafer components instead of pins, wafer tumbler locks are commonly found in applications like car doors, filing cabinets, and light commercial hardware. When the correct key is inserted, the wafers align to allow the lock cylinder to rotate.

Wafer Tumbler Lock
When no key is present, the wafer stacks (red) are pushed downward by their springs. In this state, portions of the wafers extend into a lower groove in the outer cylinder (green), mechanically locking the plug (yellow) and preventing it from turning.

Inside the Wafer Tumbler Lock
When the correct key is inserted, its specific profile lifts each wafer up. The wafers are raised just enough to move out of the lower groove in the outer cylinder but not so far that they enter the upper groove, aligning their edges with the boundary between the plug and cylinder.

Wafer Tumbler Lock with Key
Once all wafers are aligned with the shear boundary between the plug and outer cylinder, they no longer obstruct the plug. In this aligned state, the key, wafer stack, and plug (yellow) rotate together, allowing the lock to open.
Disc Detainer Locks / Disc Tumbler Locks:
These locks use a set of rotating discs with notches that must be aligned by a specifically shaped key to release the mechanism. Disc tumbler designs are often more resistant to picking than simple pin or wafer locks and are used in higher-security situations and outdoor environments. However, picking such lock is not impossible but typically requires dedicated tooling.

Pin Tumbler (left) & Disc Tumbler Keyholes (right)
Notice the visible differences between the keyholes of the standard pin tumbler lock and the disc tumbler.
When the correct key is inserted and turned, each disc rotates to a precise angular position. In this configuration, the notches cut into the perimeter of the discs align to form a continuous channel. This alignment allows the sidebar to drop from the cylinder into the channel created by the aligned notches, removing any obstruction to rotation. With the sidebar fully seated, the cylinder is free to rotate, disengaging the locking mechanism and opening the lock.
If an incorrect key is used, even a single disc will be rotated to an improper angle. Its notch will fail to align with the others, preventing the formation of a continuous channel. As a result, the sidebar remains engaged with the disc pack, blocking cylinder rotation and keeping the lock securely locked.
For the purposes of this article, profiles like dimple locks, safes, combination-based locking systems etc are not covered. These mechanisms operate on fundamentally different principles than most keyed mechanical locks and often involve distinct designs, threat models, and attack techniques. As such, they are considered outside of the intended scope of this overview.
Picking and Bypassing
As we mentioned earlier, locks are often a balance between security and cost. Therefore, trade-offs in materials, manufacturing tolerances, and design complexity can limit the effective security of common locking mechanisms making them vulnerable. Existing Vulnerabilities are often systemic, affecting entire categories of locks rather than individual models.
A significant factor directly driven from cost is manufacturing tolerance. For example locks must allow small clearances between internal components to function reliably. In low-cost, mass-produced locks, these tolerances are often wider than intended, reducing effective variation between units and making them more susceptible to bypasses.
Lockpicking and bypass techniques represent two broad approaches to defeating locking systems. Methods such as traditional lockpicking, key bumping, tryout keys, and comb picks all work by interacting-directly or indirectly-with a lock's internal components, exploiting design characteristics, tolerances, or predictable behavior to place the mechanism into an unlocked state. While these approaches differ in tools and dynamics, they share the common goal of overcoming the locking function either from within the cylinder or by leveraging weaknesses outside the primary locking interface.

Sample Lock Picking Sets
Common Techniques
Lock manipulation can be approached in many different ways, and there is no single technique that works best in every situation. Most practitioners develop their own preferred styles based on experience, lock design, and available tools. The most common methods are showcased below but before visiting each one of them we should cover the basic alignment and usage of tools.
Tool alignment and control matter more than force. The hook is typically oriented so its working surface can clearly feel individual pins (pointy edge facing up).
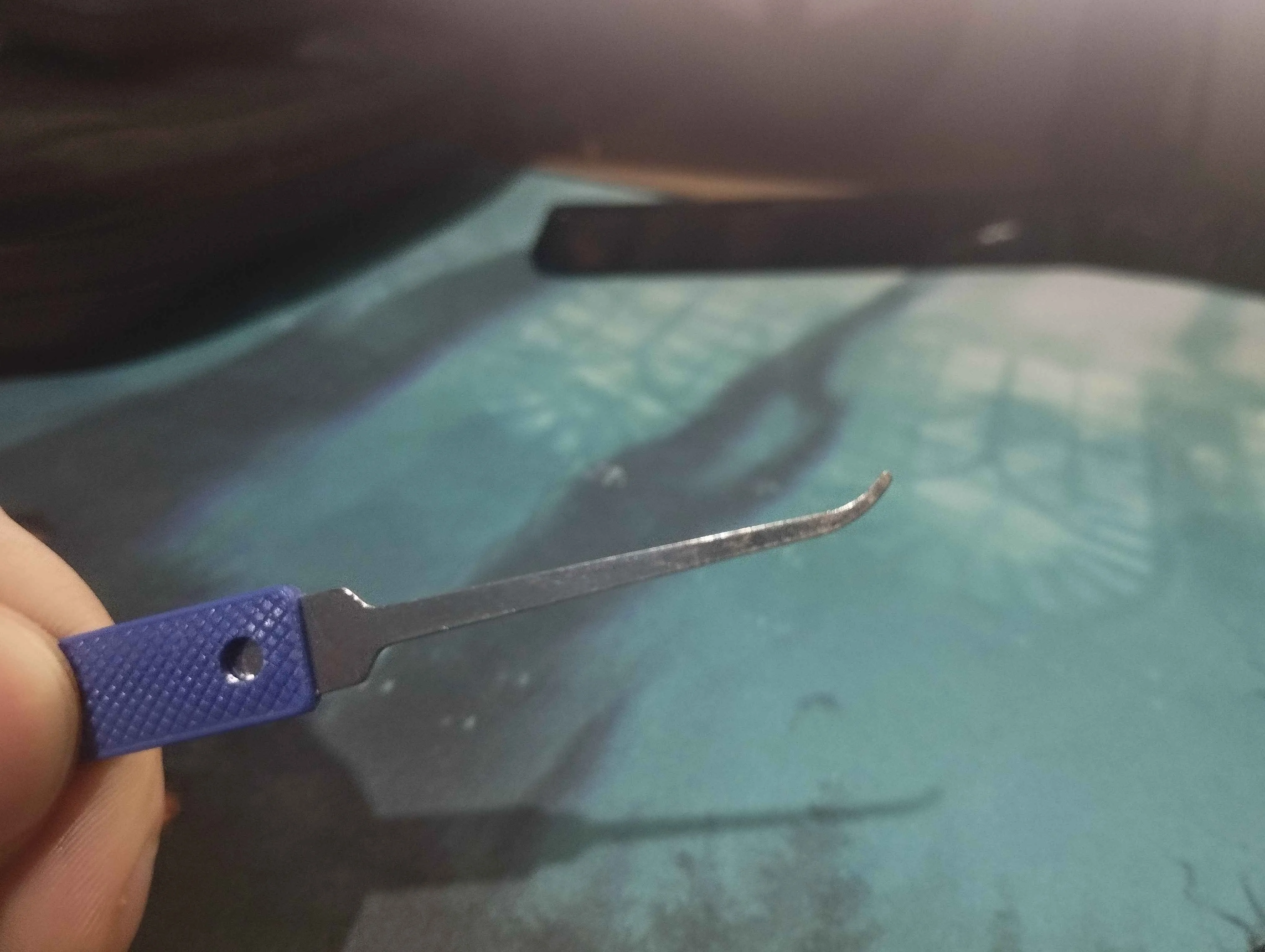
Correct Hook Alignment
Same principle applies for rakes: keep the tool comfortably aligned so it moves freely through the keyway, while maintaining light, steady tension for feedback. Many snake rakes are intentionally usable in both orientations to provide different profiles.

Snake Rake Alignment
Last but not least, tension wrenches work best when they're treated as control tools rather than sources of force. Use the lightest pressure that still allows feedback from the lock, keeping the wrench stable and out of the way so it doesn't interfere with the pick. Consistent, minimal tension improves feel and precision, while excess pressure quickly reduces feedback and makes progress harder instead of easier while also many times blocking your progress completely.
Note that in order to actually pick the lock you must identify the correct way to turn the chamber. This can be easily done by inserting and turning the tension wrench left and right. The direction providing the most resistance will be the wrong one. Notice how the chamber turns just a little bit on the correct direction when minimal force is applied. Hence in this example we should apply tension clockwise.

Example Tension Wrenches
Tension Direction
Single-Component Picking:
This approach focuses on interacting with one internal component at a time, treating each element as part of a constrained mechanical system rather than as an isolated obstacle. The objective is to observe how individual components respond under rotational load and to identify their required alignment within the locking mechanism.
A defining characteristic of this method is its reliance on mechanical feedback. When rotational force is applied to the plug or core, small variations in manufacturing tolerances cause internal components to bind unevenly. These binding conditions reveal information about which component is resisting movement at a given moment. By incrementally correcting these misalignments, the mechanism can be progressively brought into an unlocked state.
Although most commonly associated with pin tumbler locks, the same principles apply to other mechanisms. In disc detainer locks, for example, individual rotating discs replace pin stacks, yet each disc must still be positioned correctly to satisfy the locking condition. The underlying strategy, isolating and aligning components based on feedback, remains the same even though the geometry and interaction differ.
Because this technique prioritizes precision and control, tools with narrow, curved profiles are typically favored. Such profiles allow access to individual components while minimizing unintended interaction with adjacent elements.
Raking Techniques:
Raking techniques take a fundamentally different approach by manipulating multiple internal components simultaneously rather than addressing them individually. Instead of seeking precise alignment through controlled adjustments, this method relies on rapidly changing the positions of internal elements in a way that approximates the motion and profile of various keys.
By applying repeated, sweeping movements, raking introduces significant positional variation among components. In locks where internal elements follow predictable layouts or exhibit wide tolerances, this motion can cause multiple components to momentarily reach acceptable alignment at the same time, allowing the mechanism to transition into an unlocked state.
Raking is often sensitive to overall lock quality and internal consistency. Locks with uniform pin lengths, weak spring pressure, or limited security features tend to respond more readily, while higher-tolerance designs reduce the likelihood of successful alignment through randomization alone.
Specialized tools exist specifically for raking, featuring profiles designed to maximize contact with multiple components at once. While generally offering less precision than single-component approaches, raking techniques can be effective when speed and simplicity are prioritized over fine control.

Raking A Pin Tumbler
Of course you can't be always lucky, by practising sweep and non-blocking movements while also applying and releasing the correct amount of tension you will eventually rake your lock.
Brute-Forcing A Pin Tumbler
The same principles apply when raking other lock profiles as well, including common door locks found on residential hardware even though keyway shapes and pin alignment is upside down.
Raking a Different Lock Profile
Miscellaneous Techniques:
Beyond these core approaches, there are several other techniques used to bypass locking mechanisms, though they are generally less common or more specialized. Some rely on energy transfer or vibration (for example Pick Guns) to momentarily align internal components, while others use specially shaped keys or tools to exploit loose manufacturing tolerances or specific design characteristics.
Finally it's worth mentioning that separate from manipulation techniques, bypass methods exist, which defeat a locking system by exploiting weaknesses in its design, installation, or surrounding hardware rather than engaging the lock mechanism directly. These can include slipping or shimming actions, manipulating latches, or interfering with internal actuators and bolts such as certain door-latch bypasses that allow a door to be opened without interacting with the cylinder at all.
Creating your first kit
Don't get me wrong, most times higher-priced items generally indicate higher tool quality. It is highly expected for low-priced items to be of poor quality. But that should not stop anyone from trying them out. And who knows, maybe we can strike some gold among trash.
Ideally the kit I want to create consists of the following tools:
- Lock Picks
- Comb Picks
- Jiggler Keys / Jiggler Lock Picks
- Warded Lock Picks
- Bypass Knives
- Padlock Shims
- Pry Bars
- Tension Wrenches
Optional additions:
- Traveler Hooks / Latch Bypass Tools
- Door Shims
I believe this kit is more than enough at the moment, covering various cases one might encounter.
All products are purchased from a well known chinese site. I will refet to it as "AE" since I don't want to write the full name here (you may base64 decode this if you still didn't get it QWxpRXhwcmVzcw==). Unfortunately product listing is frequently changed and links might break so I will try to provide pictures of the products instead.
Item review:
The first item in the list can't be other than the very basic "Lock Pick Set". They come in many forms depending on the price, usually including 12 to 24 tools (different type of rakes, hooks, extractors etc) and 1 to 3 tension wrenches or pry bars.
The cheapest solution going under 10$ includes:
- 2 Long Rakes
- 3 Bogota Hump Rakes
- 3 Hooks (With simple tips like short hook and gonzo hook)
- 2 Diamond Hooks
- 1 Full Snowman
- 1 Key Extractor (Not really a picking tool but helpful for extracting broken keys or tool parts)
This set also includes:
- 2 Tension Wrenches
- 1 Auto Tension Tool
- 1 Polyurethane Leather Case

Your first and very basic Lock Pick Set
This set in my opinion is a great first entry on our toolbox. However as expected from the corresponding price, such pick sets are usually made from low-grade stainless or stamped spring steel which makes them inexpensive but bendy and breakable when forced. The tension tools are also very thin and given the material quality in mind they should be replaced immediately. Finally a little sanding could really help the rough edges on hooks and rakes to become slightly more curved. This helps the tool to slide easily since they tend to "jam" if the surface is too spike-y.
A slightly more expensive set (might be labeled as "GOSO" even if it's not) around 10$-20$ includes:
- 6 Hooks
- 1 Shallow Half Diamond
- 1 Half Snowman
- 1 Hollow Half Diamond
- 1 Dimple Lock Rake
The set also include 10 "weird" picks/rakes you may never even use but they are useful for automotive locks (also includes a large Y wrench tension tool for the same cause). The whole kit comes in a cool zip case with two layers handy enough to organize the picks in any way you like. The materials used overall are also cheap but a little thinner than the more affordable solution which is good for quality but might make the tools harder to insert in some locks. PS, two wanna-be tension wrenches are also included but I believe they don't even deserve to be mentioned since I find them impractical.

A slightly larger Lock Pick Set
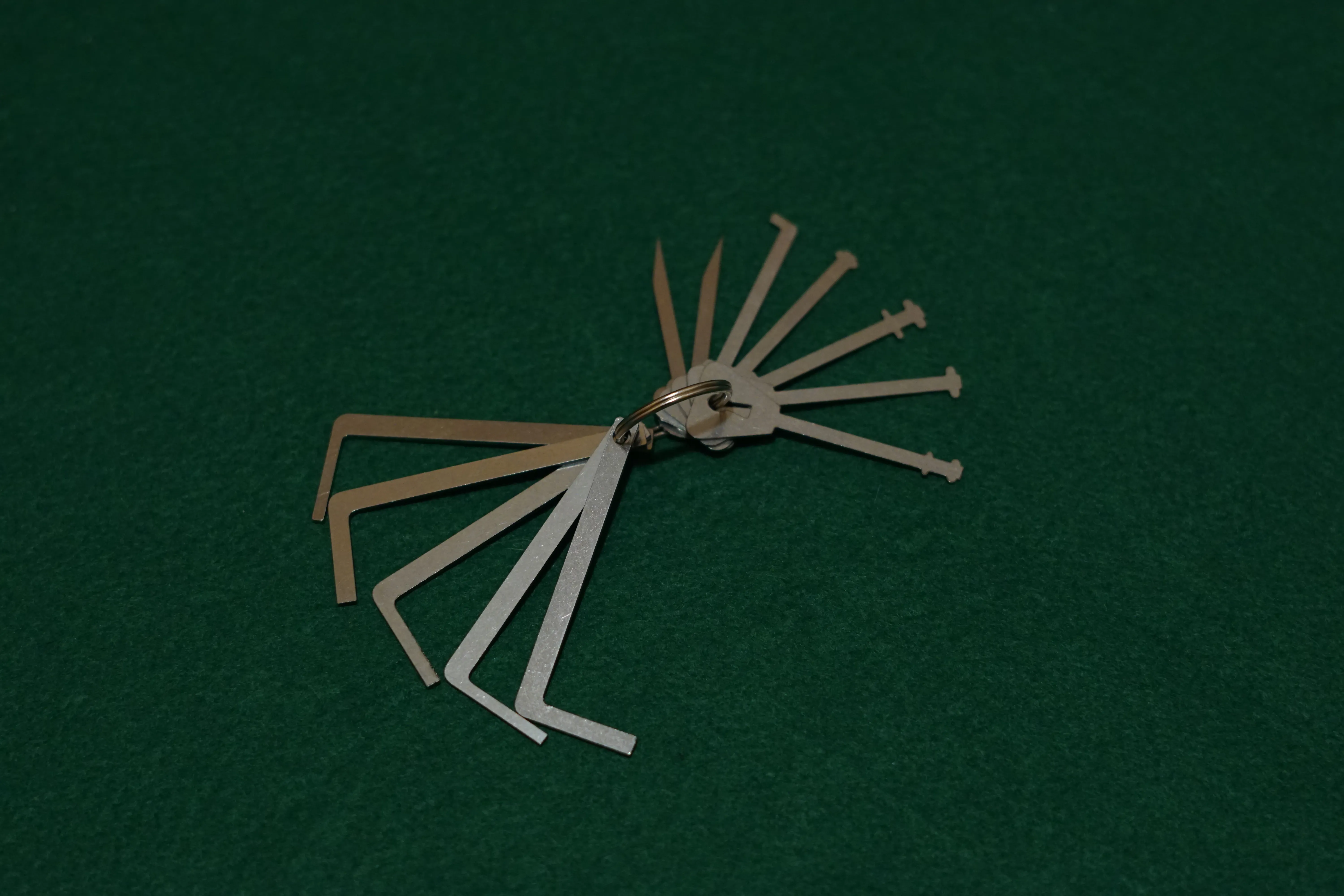
The third set I want to showcase is a mixed collection mostly consistend of different rakes under the 15$ category. 10 "mini" rakes of multiple shapes are included along with 5 tension tools (with extra comb picks at the edges or even a tension tool for tubular locks). Most specifically you can find:
These rakes are thin, small in size and might be difficult to operate but I find some of them (like the four-hump bogota rake) very useful and easy to carry around. The edges on most of them however are very sharp and they could use a little sanding. The tension tools even though not perfect are decent enough and the comb edge is a nice addition but I haven't found a use case for them yet.

Small Rake Set
Next to the list is a keychain composed of Jiggler Keys / Jiggler Lock Picks. A lot of profiles are included inside. The set includes 10 pieces and it's a nice addition for under 4$. Depending on the lock itself, some profiles are very usefull, some are not - as expected. The only downsides I can notice are the sharpness on the end of the keys. When you try to rake a lock with them it's really easy to cut yourself if not careful enough. Can be easily tackled by applying a layer of tape around them.

Jiggler Keys
Jiggling a Padlock
Another keychain I also tried containing of skeleton keys, warded picks, and two small utility knives comes with bonus tension tools but to be honest I've never used them. Maybe the most interesting inclusions are the Multi-Wheeled Combination Lock knives. They are super thin in order to fit in between the combination dials and release the shackle by pushing the bar inside. Can also be found under 7$.
Multi-Purpose Keys
Upcoming in the list we have 2 different multi-tools built like a pocket knife around 10$ each. Both of them come with a tension rod which upon removing "frees" the picks. You can pull out one or your liking and tight it with a screw on the side. The first case is a nice to have every-day-carry gadget but not a necessity since it does not provide more than what we already have in the lock pick sets above.
The second case in my opinion is a waste of money. The picks are too slim, the edges are too short. Completely useless. The products comes with many pieces to replace (around 24 shapes) but sadly it cannot replace the money you lost.

Multi-Tools (bad one on the left, better product on the right)
Lastly some decent inclusions are: The comb picks, the padlock shims and these "weird" picks for large keyholes commonly found on interior doors (can be found named as "Mortice Locks"). I bundle these three together since each has a very specific use case but you really can't go wrong manufacturing these. Comb picks are rarely used, they were primarily effective against older, low-tolerance pin-tumbler locks that lacked modern security features. Over time, lock manufacturers introduced anti-bypass mechanisms, such as shorter pin stacks. These improvements make the simple "overlifting" technique of a comb pick ineffective on most modern locks. The set we purchased comes with 7 combs with different "teeth" for around 5$.

Comb Picks
The padlock shims (even though not a pick but a bypass tool instead) is a slender, often metal (but also found in slim plastic) tool designed to interact with the shackle-retention mechanism of a padlock in order to release the shackle without using the original key. Shims are sized and shaped to fit into the gap between the shackle and the padlock body. The set we purchased comes with 10 pieces of shims in multiple shapes.

Padlock Shims

Padlock Shims Inserted
Finally the Mortice lock pick set which comes with 2 pieces (for 3$) is a simple construct, basically even a bended iron rod could do the work. Most interior locks are very simple to "pick", you just need a right-sized tool to insert in the keyhole and turn the mechanism.
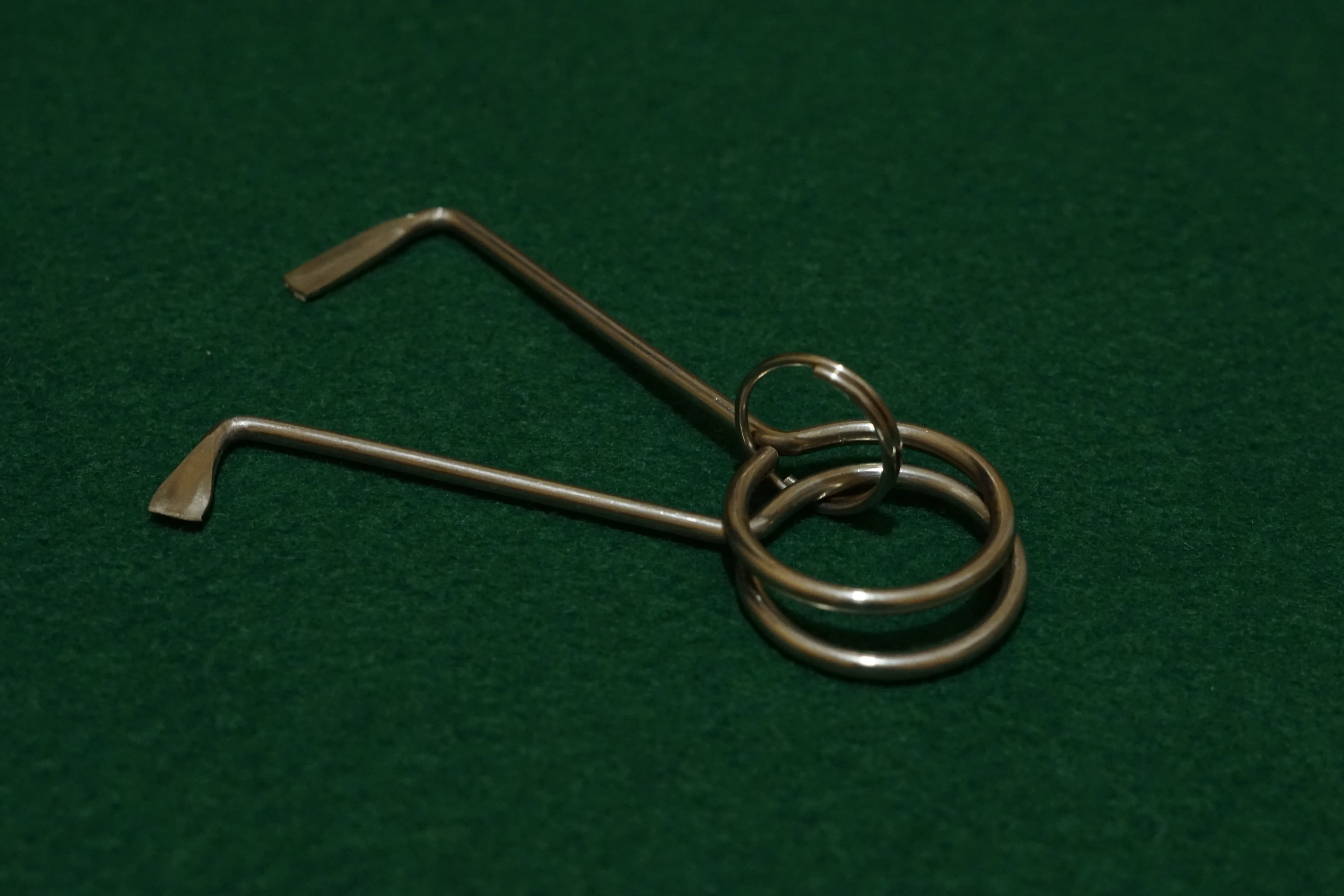
Mortice lock picks
Final Kit Evaluation
Taken together, the tools reviewed above form a well-rounded, full-capability beginner kit capable of addressing a wide range of common lock manipulation and bypass scenarios. While this approach deliberately avoids the highly priced tooling often marketed by well-known brands, it demonstrates that practical coverage can still be achieved by selectively combining low-cost alternatives even at the expense of some material refinement and long-term durability.
By prioritizing functional diversity over premium finishes, the resulting kit includes hooks, rakes, jigglers, comb picks, shims, and bypass-oriented tools sufficient for exploring multiple lock types and attack categories. The trade-offs are clear: softer materials, thinner tension tools, and the need for occasional finishing or replacement. However, none of these limitations fundamentally prevent effective experimentation or learning.
Based on current pricing across the components discussed, the total cost of the complete kit comes to approximately $70 USD, a fraction of the price typically required for a similarly comprehensive setup built exclusively from premium offerings. For beginners or security researchers looking to explore physical security concepts without a significant financial barrier, this represents a pragmatic and accessible starting point. Of course it is not necessary to purchase all the items in the list to begin your journey, for starters even the cheapest pick set will suffice. However as you keep exploring different lock profiles you might find a toolkit expansion inevitable.
It is important to understand that not every tool discussed in this article is required to begin practicing lock picking. A minimal and effective starting setup consists of just three components: a basic hook and rake set, a small selection of quality tension wrenches (preferably purchased separately, as those included in cheap kits are often inadequate), and a single practice lock. This combination is sufficient to learn fundamental manipulation techniques, develop tension control, and understand feedback without unnecessary complexity or expense.
Practice makes perfect
If you want to throw a little more money in the pot consider purchasing a dedicated practice lock set. Such set is one of the most valuable learning aids for anyone starting out in lock picking. Sets that include multiple lock profiles such as pin tumbler, wafer, and basic padlocks allow beginners to experience how different mechanisms feel under manipulation and to recognize variations in feedback, resistance, and tolerance. Transparent or cutaway practice locks can be especially useful early on, as they help visually correlate tool movement with internal component behavior.

Practice Lock Set
A note for Safety, Ethics & Legal Considerations
Before acquiring or using lock-picking tools, it is important to understand that legal treatment of such equipment varies significantly by country and jurisdiction. In many places, ownership is legal when there is no intent to use the tools unlawfully, while in others, possession alone (or carrying tools outside a private setting) may be restricted or criminalized under burglary-tool statutes. Enforcement often depends on context, intent, and local interpretation of the law. As a result, anyone interested in lock picking should familiarize themselves with the applicable regulations in their area and ensure that all experimentation is conducted only on locks they own or have explicit permission to manipulate. Responsible practice is essential not only for legal compliance, but also for maintaining the ethical standards expected in legitimate security research.
Closing
At its core, lock picking is not about defeating locks for their own sake, but about understanding the limitations and assumptions built into physical security systems. Exploring these mechanisms with affordable tools reinforces an important lesson familiar to anyone in cybersecurity: weaknesses are often systemic, cost-driven, and repeatable. By experimenting with low-cost equipment and common locks, beginners can gain valuable insight into real-world security trade-offs while developing responsible research habits.
Whether you pursue lock picking as a casual hobby or as a complement to security research, a simple budget kit is often more than enough to take the first steps. In case you want to watch a more detailed analysis on showcased tools and techniques, I created a frequently updated playlist with videos from far more experienced lockpickers.
Closing, I would like to thank a friend wishing to remain mysterious™ (his words) for helping with the photo shoot and of course the host of this article i0.rs. Until next time!